Before the COVID-19 outbreak, we thought we understood just how much technology was changing the modern world. But, over the last few weeks and months, we’ve learned a lot about all the wonderful capabilities of digital life and discovered some of its limitations. As we start thinking about what life looks like during and after the recovery phases of this pandemic, organizations may need to make some adjustments. Just how should your IT strategy and technology stack evolve from there? It’s different for every business, but most companies are asking similar questions: First, how can we make sure our technology infrastructure can support our remote workers? How well do our security systems and processes stack up? And, finally, after stay-at-home orders relax, will some individuals continue working remotely, and can we handle that?
How well did communication tools support the team?
Today, more than ever, it’s clear that Unified Communications (UC) platforms and collaboration tools are the lifelines of successful remote working. Now is an excellent time to ask yourself – how well did our UC tools support employees? Were there gaps in service? Did employees have to give out their cell phone numbers to customers? Did teams use FreeConference or Google Hangouts, or other consumer-grade tools to connect?
If yes, it may be time to look into enterprise-grade UCaaS or cloud-hosted VoIP solutions that offer more security features and functionality. The good news is that with a hosted voice solution all of the management and maintenance responsibilities are transferred to the service provider, instead of companies having to install IP-PBX equipment at each business location. This is a big deal, especially going forward if your IT staff is restricted to working remotely as well. Hosted VoIP solutions also deliver advanced communication features that make it feel like employees are still working from their office desk, such as an auto-attendant, call forwarding, DID calling, voicemail to email, and much more.
Did the security framework extend to at-home working?
Maintaining network security has been primarily a piece-meal approach for most companies during the course of the last several months. That’s because we’re asking so much more from our IT security and data protection systems. Most organizations also have more applications and endpoints to secure than ever before. With so many priorities to juggle when it comes to security, company leaders should focus on the basics first, including evaluating administrative and technical security controls. Here are some best practices to keep in mind.
- Administrative controls – When people talk about administrative security controls, it’s usually referring to the ‘human factors’ that contribute to security. Examples include procedures or guidelines that outline what network resources and assets employees have access to, the level of access, and managing these things within the business framework. As some individuals come back to work over the next several weeks and months, IT leaders may have to adjust these controls to keep up with current conditions. To reduce a company’s security risk, leaders should also classify resources to minimize access to the most sensitive assets. For organizations that will keep a large part of their workforce at home, teams should also communicate with employees frequently to help them maintain risk awareness, as secure habits may recede over time. Business leaders can reference FTC guidelines and other resources to remind employees about security procedures, and how to spot common ransomware or phishing attacks, for example.
- Technical controls – Technical controls are the hardware and software IT teams use to protect assets. This category can include next-generation firewalls (NGF), intrusion detection systems, secure networking equipment, anti-malware and ransomware protection, VPNs, and two-factor authentication. Requiring up-to-date anti-virus security software on employee devices can go a long way in protecting corporate assets. Utilizing mobile device management programs is also helpful. Mobile management software can help IT enforce strong passwords and data encryption, and can set limits on app installation, offer remote wipe capabilities, and more.
In the case of having more employees at home, IT can help workers better secure their home networks with password protection. In some cases, home internet providers also offer security protections using advanced analytics and AI technology to monitor and analyze WiFi traffic, automatically blocking suspicious activity. Offering to bump up the use of these at-home network monitoring tools during this time can help protect a company’s data, applications, and assets.
Small tweaks can yield big returns
As we come out of the ‘crisis phase’ of COVID-19 and move into the recovery stages, companies have a great opportunity ahead of them. It’s an ideal time to evaluate how well your technology stack keeps up with having more remote workers. Plus, it’s a great time to identify areas for improvement. Now more than ever, by relying on a robust cloud communication platform and strong security policies, teams can stay connected, while securely maintaining their company’s digital assets.
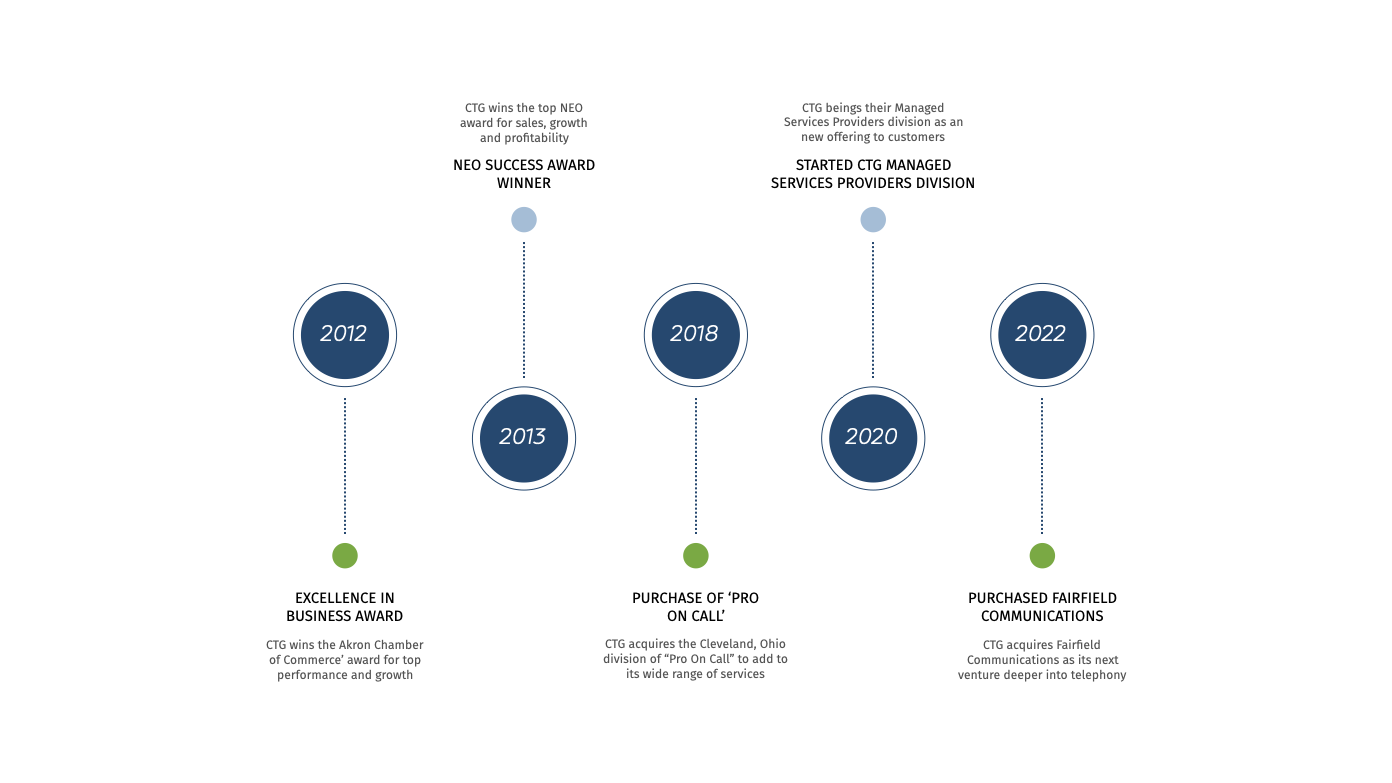
If you want help putting a plan together for your IT infrastructure that meets your needs and budget, talk to CTG. By relying on our skilled IT staff, we can architect and implement your optimal technology stack that has the efficiency and scalability to navigate this challenging climate. Don’t wait to make even small changes now that can make your technology stack much stronger and more agile in the coming months – let’s do this!